@cryptyk - Maybe you have posted on this earlier in this thread, and if so please post a link, but what are the security implications of entering your password into the evmote web page? Is the password stored anywhere or do you just get an oAuth token?
Welcome to Tesla Motors Club
Discuss Tesla's Model S, Model 3, Model X, Model Y, Cybertruck, Roadster and More.
Register
Install the app
How to install the app on iOS
You can install our site as a web app on your iOS device by utilizing the Add to Home Screen feature in Safari. Please see this thread for more details on this.
Note: This feature may not be available in some browsers.
-
Want to remove ads? Register an account and login to see fewer ads, and become a Supporting Member to remove almost all ads.
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
EVmote App
- Thread starter cryptyk
- Start date
-
- Tags
- Model S User Interface
skialpine
Member
I have been trying to update my password as I had changed it on my.teslamotors however each time I do it the site appears to crash and is unavailable to me for .
Here is the latest error message, I have seen this several times yesterday and today.
You
San Jose
www.evmote.com
Here is the latest error message, I have seen this several times yesterday and today.
Error 524 Ray ID: 261091d9e6441ecb • 2016-01-07 15:08:41 UTC
A timeout occurred
You
Browser
WorkingSan Jose
CloudFlare
Workingwww.evmote.com
Host
Error
I have been trying to update my password as I had changed it on my.teslamotors however each time I do it the site appears to crash and is unavailable to me for .
Here is the latest error message, I have seen this several times yesterday and today.
My bad. This is fixed now.
- - - Updated - - -
@cryptyk - Maybe you have posted on this earlier in this thread, and if so please post a link, but what are the security implications of entering your password into the evmote web page? Is the password stored anywhere or do you just get an oAuth token?
I'm glad you asked.
When you put your password into EVmote, I immediately send it over to Tesla and exchange it for an Oauth token. I store that Oauth token in your user account and use it to request your information from the Tesla APIs. There are also other tokens used for streaming GPS data. I *never* store your MyTesla password. I don't store it to disk, I don't log it, and I don't store it to the database.
Your Oauth token can become invalid for a couple of reasons: because it expired after a few months, or because you changed your MyTesla password. EVmote detects when this happens and sends you an email letting you know that you need to come back and re-enter your MyTesla password. Again, I use that only to get a refreshed set of tokens.
As for your EVmote password, that's hashed and salted, and again, never stored as clear text.
If you ever want to delete your EVmote account, there's a button on the My Account page. This will remove ALL of your data from the database, including your trip data (GPS data). The only information that will remain is the log data which contains your email address and your actions on the site. Those will be deleted 15 days later, as the logs are rotated.
Hope that helps,
Ryan
skialpine
Member
Thanks Ryan - I was guessing that is what happened but I just wanted to make sure.When you put your password into EVmote, I immediately send it over to Tesla and exchange it for an Oauth token. I store that Oauth token in your user account and use it to request your information from the Tesla APIs. There are also other tokens used for streaming GPS data. I *never* store your MyTesla password. I don't store it to disk, I don't log it, and I don't store it to the database.
One follow-up question that I just thought of - are the tokens encrypted? If not then if someone got a copy your database then couldn't they issue commands to our cars?
Last edited:
1NJ85D
Member
Ryan,
I am a happy user of eVmote's IFTTT integration. More specifically, I leverage Amazon Echo --> IFTTT --> EVMote ---> Tesla and tell Amazon Echo to turn on Climate Control when I am about to leave the house in the morning. The caveat is that this does not work when the car is asleep. In other words, EVMote's URL automation commands only work when the car is awake. Would it be possible for you to test if the car is asleep and wake it up if needed before issuing the requested command?
Thanks much, Antonio
I am a happy user of eVmote's IFTTT integration. More specifically, I leverage Amazon Echo --> IFTTT --> EVMote ---> Tesla and tell Amazon Echo to turn on Climate Control when I am about to leave the house in the morning. The caveat is that this does not work when the car is asleep. In other words, EVMote's URL automation commands only work when the car is awake. Would it be possible for you to test if the car is asleep and wake it up if needed before issuing the requested command?
Thanks much, Antonio
Thanks Ryan - I was guessing that is what happened but I just wanted to make sure.
One follow-up question that I just thought of - are the tokens encrypted? If not then if someone got a copy your database then couldn't they issue commands to our cars?
Sorry - I didn't see this edit until just now. There are multiple layers of protection here that I'll outline below. I appreciate your concern. I'm not sure that everybody realizes what it means to give your Tesla password to a third party (such as myself). Anyone with your password can get your GPS coordinates, unlock your car, start it, and drive away. This is part of the reason we all wish that Tesla would implement an Oauth2 system with scoping so that users could get the benefits of a third party development solution without the risks associated with giving away the farm. At this point, you have to really trust whoever you give your password to.
So first: Why should you trust me?
Well, I'm a professional software engineer with over 25 years of experience. I've worked on projects for law enforcement, homeland security, and for the private financial industry. I currently work on a project that has access to hundreds of millions of financial documents. Here's my resume: www.ryansteckler.com. This isn't to say that EVmote is invulnerable, because nothing is perfect. This is not my first rodeo, however. While I'm a bit cavalier about things like unit tests and uptime on my side projects, I don't compromise on security.
So, here is how your Oauth token is protected by a multi-layer pattern:
Encryption at rest: The entire disk that contains the database is encrypted. This ensures that if someone were to sneak into Amazon and steal the physical disk, they couldn't do anything with it.
Application-level field encryption: The Oauth token is encrypted by the application before it's stored in the database. This uses aes-256-cbc encryption, plus a random salt.
Network-level encryption: The applications only communicate with the database over SSL.
Strong authentication on the database: Only authorized users can access the database, and those credentials and keys are stored securely.
Network security: The database servers are not on the Internet. They're only accessible from the application servers. The application servers are only accessible to the internet via HTTP and HTTPS. When I need to work on any of those boxes, I use a bastion (jumpbox), then selectively allow access between the bastion and the target server for only the duration of the maintenance.
Credential security: Keys are never checked into source control or committed to disk.
Log Security: Sensitive information is never logged to disk or to analytics platforms (like ElasticSearch)
Algorithmic security: I don't write my own encryption algorithms or get "creative" with security. These are things best left to the experts and mathematicians. I'm happy just following industry best practices.
There are other things as well, but those are some of the big ones. At the end of the day, anything is hackable. I'm just here to make sure it's really, really, really hard to hack EVmote
Thanks,
Ryan
- - - Updated - - -
Ryan,
I am a happy user of eVmote's IFTTT integration. More specifically, I leverage Amazon Echo --> IFTTT --> EVMote ---> Tesla and tell Amazon Echo to turn on Climate Control when I am about to leave the house in the morning. The caveat is that this does not work when the car is asleep. In other words, EVMote's URL automation commands only work when the car is awake. Would it be possible for you to test if the car is asleep and wake it up if needed before issuing the requested command?
Thanks much, Antonio
Good call. I've added this to the list.
cynix
Member
When you put your password into EVmote, I immediately send it over to Tesla and exchange it for an Oauth token. I store that Oauth token in your user account and use it to request your information from the Tesla APIs. There are also other tokens used for streaming GPS data. I *never* store your MyTesla password. I don't store it to disk, I don't log it, and I don't store it to the database.
Hi Ryan, is it possible for a user to request the token from teslamotors.com themselves and only provide the token to EVmote?
Hi Ryan, is it possible for a user to request the token from teslamotors.com themselves and only provide the token to EVmote?
It's possible, yes. It's not something I'll include in EVmote in the near term, though. It would require the user to "go find" the Tesla API keys and make a couple of HTTP calls with curl/wget, then copy the key onto EVmote. That's not something I think most people want to deal with. In the end, you're still providing the key that allows EVmote to control your car, so the only additional benefit of doing it this way is that your password never traverses the EVmote system. It turns out that passwords are actually much easier to handle than Oauth2 tokens because of some fancy math.
What you're talking about is EXACTLY what Tesla should build though, and there are already a half-dozen standards for doing it. Think of it like Facebook: When you want to connect your Facebook account to another website, you don't need to give your FB credentials to the site directly because FB has created a legitimate Oauth2 flow.
I've actually thought of making an Oauth2 front-end for Tesla and letting other developers use it. That way, at least you would only be giving one site the password instead of multiple. And it's small enough that it could be easily open-sourced, etc. Maybe I'll pick that back up in my "free" time
Thanks,
Ryan
Last edited:
1NJ85D
Member
Ryan,
I am a happy user of eVmote's IFTTT integration. More specifically, I leverage Amazon Echo --> IFTTT --> EVMote ---> Tesla and tell Amazon Echo to turn on Climate Control when I am about to leave the house in the morning. The caveat is that this does not work when the car is asleep. In other words, EVMote's URL automation commands only work when the car is awake. Would it be possible for you to test if the car is asleep and wake it up if needed before issuing the requested command?
Thanks much, Antonio
Ryan. Thanks for adding this to your list. On a "tactical" basis, could you maybe add the Wake command to your list of available HTTP calls. I could use IFTTT or something similar to keep the car awake in those periods when I am more likely to need it to be awake. Thanks. Antonio.
Ryan. Thanks for adding this to your list. On a "tactical" basis, could you maybe add the Wake command to your list of available HTTP calls. I could use IFTTT or something similar to keep the car awake in those periods when I am more likely to need it to be awake. Thanks. Antonio.
Done. You shouldn't need to keep the car awake. You should be able to just issue the wakeup command before the others. You don't really have a way to check if the car is awake (because you can get the "sleeping" code from IFTTT when it calls my API), so I would issue "Wake Up", then wait 60 seconds, then issue your chosen command.
Thanks,
Ryan
Hi Everyone,
I hope you've been enjoying EVmote! I want to start by thanking all of the folks who have been helping out during the beta. This thread is 28 pages of your feedback, suggestions, and bug reports. You've helped make EVmote what it is today!
I started this project because there were things I wanted our cars to do that they weren't capable of with Tesla's apps. Today, EVmote lets you:
I really enjoy building software. It's my passion. I love it so much that I've been spending all of my free time and paying for servers so that hundreds of us could enjoy the features of EVmote. At this point, I'd like to see if EVmote provides enough value that you're willing to share in those expenses.
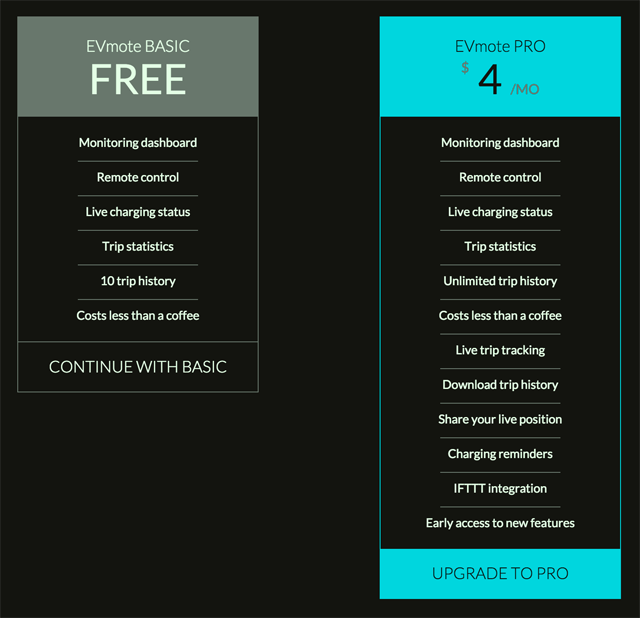
Starting later today, EVmote will have a Basic plan that is free, and a Pro plan with additional features. You can see the breakdown here.
Like I said, I really enjoy working on EVmote, and I hope you enjoy using it.
Thanks,
Ryan
I hope you've been enjoying EVmote! I want to start by thanking all of the folks who have been helping out during the beta. This thread is 28 pages of your feedback, suggestions, and bug reports. You've helped make EVmote what it is today!
I started this project because there were things I wanted our cars to do that they weren't capable of with Tesla's apps. Today, EVmote lets you:
- See all of your trips with statistics so you can tell if the Valet took the car out for a joyride
- Monitor and control the car from a laptop or phone, from anywhere
- Share your live location with friends and family so they know when you'll arrive
- Download all of your trip history in an Excel file so you can generate your own analysis
- Setup charging reminders in specific locations that email you when you forgot to plug in your car
- Automate your car with IFTTT
- Do all of this from a hosted web application so you don't have to install any software
I really enjoy building software. It's my passion. I love it so much that I've been spending all of my free time and paying for servers so that hundreds of us could enjoy the features of EVmote. At this point, I'd like to see if EVmote provides enough value that you're willing to share in those expenses.
Starting later today, EVmote will have a Basic plan that is free, and a Pro plan with additional features. You can see the breakdown here.
Like I said, I really enjoy working on EVmote, and I hope you enjoy using it.
Thanks,
Ryan
ArtInCT
Always Learning
Ryan:
Can you explain the IFTTT integration and what it is and what it will allow me to do?
Thanks
Art
Can you explain the IFTTT integration and what it is and what it will allow me to do?
Thanks
Art
Sure. For the benefit of folks who may not know what IFTTT even is, I'll start at the beginning 
IFTTT (If-This-Then-That) is a free service that lets people setup "recipes" that automate stuff. For example, you can have recipes that say:
"If it's going to rain tomorrow, email me the weather report"
"If the GOOG stock drops 3% in a day, set my office lights to red"
"If the temperature in my house gets above 80 degrees, log the temperature to a spreadsheet in Google Drive"
This requires two things: An "IF" and a "THEN". Both of those things need to be connected to the Internet. The good news is that your Tesla is connected!
So: EVmote's IFTTT integration lets you create recipes like:
"If I text 'UNLOCK' to IFTTT, unlock my Tesla"
"If the temperature in the morning reaches 80 degrees, turn on the AC in my Tesla"
"If I tell my Amazon Echo to 'Open the sunroof', it will open the Tesla sunroof"
"If my home security alarm goes off, honk the horn of my Tesla"
"If I'm arriving home, close the sunroof of my Tesla"
"When I pull into my garage, open the charge port" (This is my favorite because the motion catches my eye and reminds me to plug in!)
..and lots more. The cool thing about IFTTT is that you get to decide what recipes you create. They have hundreds of "IF"s, and I've added the ability for your Tesla to be a "THEN".
Thanks,
Ryan
IFTTT (If-This-Then-That) is a free service that lets people setup "recipes" that automate stuff. For example, you can have recipes that say:
"If it's going to rain tomorrow, email me the weather report"
"If the GOOG stock drops 3% in a day, set my office lights to red"
"If the temperature in my house gets above 80 degrees, log the temperature to a spreadsheet in Google Drive"
This requires two things: An "IF" and a "THEN". Both of those things need to be connected to the Internet. The good news is that your Tesla is connected!
So: EVmote's IFTTT integration lets you create recipes like:
"If I text 'UNLOCK' to IFTTT, unlock my Tesla"
"If the temperature in the morning reaches 80 degrees, turn on the AC in my Tesla"
"If I tell my Amazon Echo to 'Open the sunroof', it will open the Tesla sunroof"
"If my home security alarm goes off, honk the horn of my Tesla"
"If I'm arriving home, close the sunroof of my Tesla"
"When I pull into my garage, open the charge port" (This is my favorite because the motion catches my eye and reminds me to plug in!)
..and lots more. The cool thing about IFTTT is that you get to decide what recipes you create. They have hundreds of "IF"s, and I've added the ability for your Tesla to be a "THEN".
Thanks,
Ryan
ArtInCT
Always Learning
mikeash
Active Member
Thanks for the info on Pro. I'm glad you're charging for advanced features, makes it more likely this service will be around longer!
Do you have any plans to add support for IFTTT triggers? I'm imagining that car location could make a good trigger. Basically take what you have with charge reminders, but instead just have it ping some URL (like an IFTTT Maker channel trigger URL) when the car enters/leaves the location.
Finally, my account seems to think I already have Pro. Is this a temporary thing for existing accounts, or has something gone wrong?
Do you have any plans to add support for IFTTT triggers? I'm imagining that car location could make a good trigger. Basically take what you have with charge reminders, but instead just have it ping some URL (like an IFTTT Maker channel trigger URL) when the car enters/leaves the location.
Finally, my account seems to think I already have Pro. Is this a temporary thing for existing accounts, or has something gone wrong?
Ryan - I'm a little slow, but could you explain what I need to do on my end to get my ECHO to talk to the Model S? Even a link to something that explains it would be all I probably need.
Thanks - Dale
Sure!
First, go create an IFTTT account. It's free.
Once you have an account, you'll need to Connect your Echo to IFTTT.
Now you need to create a recipe that uses your Echo as the "This" trigger. You'll also want that recipe to use EVmote as the "Then" action.
I don't know exactly what the options are for the Echo because I don't have one, but here's a quick video I made of me setting up an IFTTT recipe with an SMS trigger that flashes my headlights on my Tesla. Hopefully that's enough to show you how it works so you can figure out the Echo-specific part.
Video:
Let me know if you need help, or if you get it working!
Ryan
- - - Updated - - -
Thanks! It would be pretty awesome if I could take my family out to dinner with some proceeds from EVmote. That might make them feel better about me ignoring them while I'm working on EVmote all the timeThanks for the info on Pro. I'm glad you're charging for advanced features, makes it more likely this service will be around longer!
Do you have any plans to add support for IFTTT triggers? I'm imagining that car location could make a good trigger. Basically take what you have with charge reminders, but instead just have it ping some URL (like an IFTTT Maker channel trigger URL) when the car enters/leaves the location.
Definitely! In fact, here is the issue in my work tracker so you can stay up to date.
Finally, my account seems to think I already have Pro. Is this a temporary thing for existing accounts, or has something gone wrong?
Everyone has a Pro account today! I wanted to deploy all of the Pro code to make sure everything is working in production with billing, etc. I've been testing it all day by actually charging my credit card, canceling my subscription, renewing, etc. I plan to make the final switch in a few hours.
Thanks!
Ryan
Last edited by a moderator:
Similar threads
- Replies
- 178
- Views
- 7K
- Replies
- 17
- Views
- 4K
- Replies
- 3
- Views
- 425


