I really wanted to know how TeslaMate works. Because… if it is able to pull all the vehicle data it might also have a way to send commands to the Tesla?
After that thought I spent some time reading the TeslaMate source code in order to figure out how the authentication works, how the Tesla credentials flow through the app and where it stored the user’s API key.
Long story short, it does save the API key where it also stores all the other data. The API key is neither stored separate nor is it encrypted.
So, if Grafana can access the vehicle data, and the API key is stored next to the vehicle data, can Grafana read and output the API key?
Well, there is
Grafana Explore to run custom queries. This needs authentication tho. What a bummer.
Ever heard about this distant cyber security issue called… “default passwords”? Yep, TeslaMate Docker’s Grafana installation comes with default credentials.
It also is possible to query the tokens as an unauthorized anonymous user without logging in through a Grafana endpoint (see CVE-2022–23126 further below as well as TeslaMate patch v1.25.1 released after private disclosure and the screenshot that is included further below).
I took the shot and tried logging in with admin:admin which, kinda unsurprisingly, but still hilariously it worked.
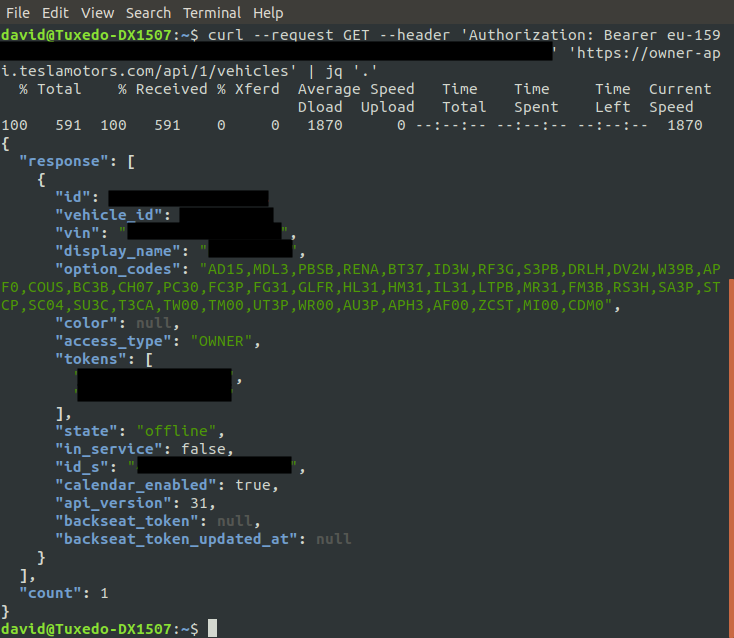
Building a Query String for Grafana (Explore) and querying the API tokens wasn’t magic after that.
That was the point where I was able to fully confirm that in this case it is indeed possible that some external attacker could do these steps and end up having substantial control over the CTO’s Tesla.
Which I deemed a high to critical security issue. No one should be able to unlock the SaaS company’s CTO’s Tesla doors… So I immediately stopped there and contacted the organization and get this resolved.